Be alert! The virus infection rate of computers and mobile terminals has increased.
CCTV News:During the 2019 National Cyber Security Publicity Week, the National Computer Virus Emergency Response Center released the 18th Survey Report on Computer Virus and Mobile Terminal Virus Epidemic.
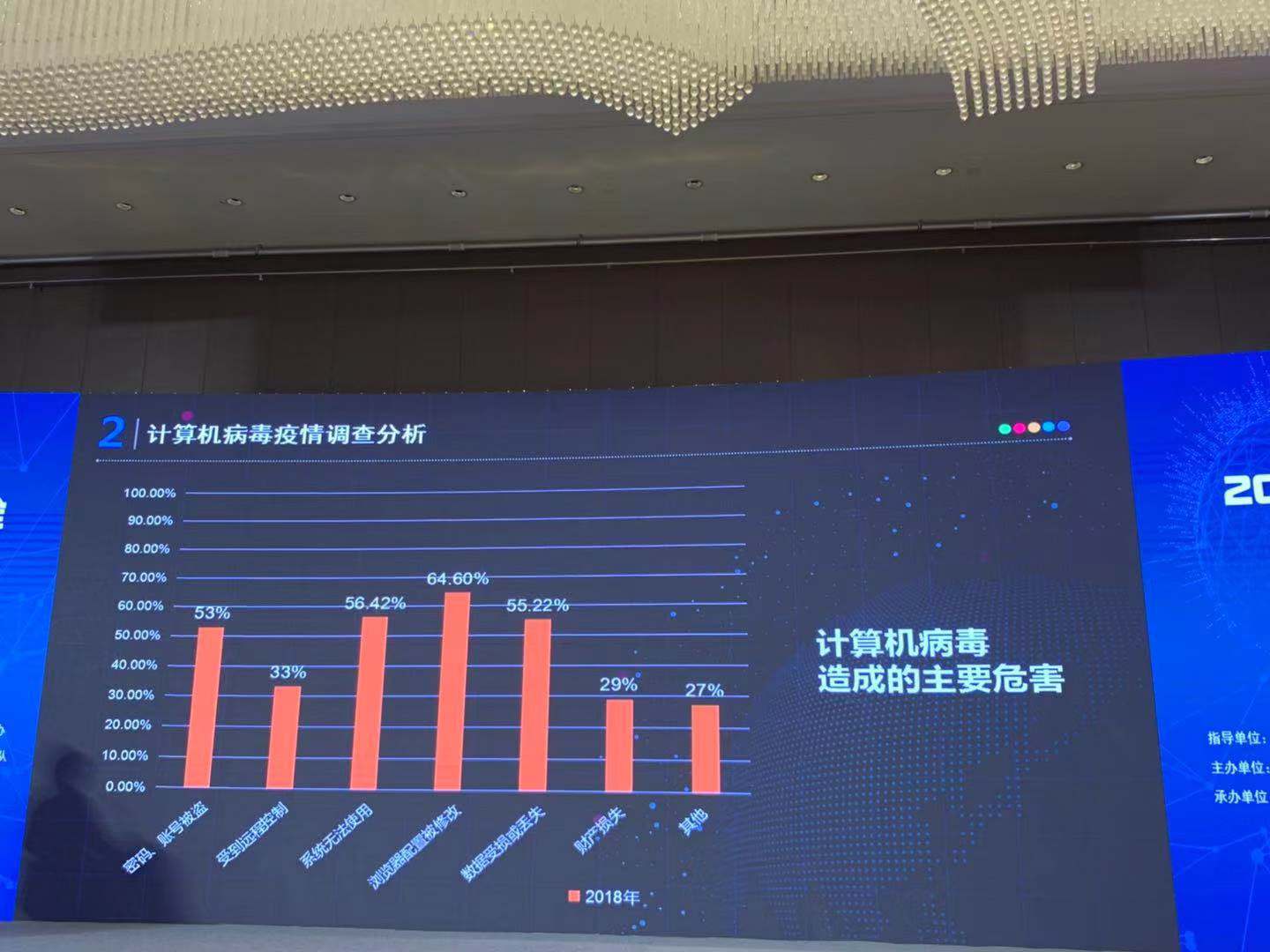
According to the Report, in 2018, both the computer virus infection rate and the mobile terminal virus infection rate in China showed an upward trend. Network security issues are characterized by variability, uncertainty, scale and fuzziness. Network security incidents become high probability events, and major network security incidents such as information leakage and blackmail virus often occur. Driven by interests, criminals in more fields have invested in mining viruses and ransomware. In order to expand the scope of transmission and counter the detection of safety products, viruses continue to update and iterate, resulting in the increase of virus number and the increase of infection rate.
Cloud mainframe has become the main target of mining Monroe coins, Eli coins and other digital currency, and "cloud mining" has risen quietly. Cybercriminals wantonly use mining software to steal the computer processing power of consumers and enterprises and occupy the cloud CPU. Malicious mining technology has been improved obviously, and the industry is becoming more mature. Malicious mining families have squeezed the value of injured computers and network equipment to a greater extent through mutual cooperation, which has brought greater challenges to security practitioners. At the same time, more and more malicious mining software is installed on the network and Internet of Things devices, which not only affects the performance of devices, but also easily forms botnets, posing a great threat to the security of the whole Internet.
The important value of data has become more and more prominent, information leakage incidents have become normal, and enterprises have weak supervision over the flow of data and access rights, which has led to the serious abuse of data by third-party plug-ins. Information leakage makes enterprises face huge compensation and threatens personal property safety and life stability. With the increasing degree of global informatization and the dependence of the whole society on network and digital technology, this situation may still intensify.
Due to the lack of security audit ability for software supply chain, supply chain pollution has become a more serious problem in the security field. For relatively tight and difficult-to-break systems and environments, criminals often look for exports in their supply chains, and the forms of attacks are various. With the development of the mobile Internet, the future of the Internet of Everything is gradually becoming clear, and there are often a large number of third parties involved in the production process of smart devices. Due to the rapid development of these third parties, they often have many problems such as doubtful development quality and unable to guarantee security performance. As one of the most dangerous and effective infection routes at present, supply chain attacks will be applied in more scenarios.
(CCTV reporter Wang Xiaopei Wang Jinglei)